
With technology accelerating, progress has been felt on both sides of the fence. To combat new-age, smarter security attacks, there arises a need for comprehensive security transformations.
Present-day data fortification and defence require a holistic approach for comprehensive security integration. Redington provides data protection infrastructure that can be optimised through intelligent software, hardware and resilient strategies.
A network device that offers security capabilities exceeding those of a traditional firewall with features such as integrated intrusion prevention, content filtering, application control and sandboxing.

A security device that protects applications, APIs and mobile application backends against sophisticated and malicious attacks through cutting-edge anomaly-detection capabilities.

A security concept that provides secure connectivity between branches, users and data centres with a centralised security policy framework.

An approach to protect the endpoints of a network like end-user devices with software that uses encryption and application control. It includes the following types:
– Endpoint Detect and Response
– Extended Detect and Response
– Next-generation Antivirus
– Encryption
– Data Loss Prevention

A system that defines and manages digital and electronic identities and regulates access to business-critical resources.
User experience is enhanced via application performance by defining individual ISP SLA (based on latency, Packet loss and Jitter) and routing application traffic through the best available ISP. This takes care of ISP load sharing, ISP failover and Active-Active link utilization besides replacing costly MPLS with Site-to-site VPN without compromising performance & security.
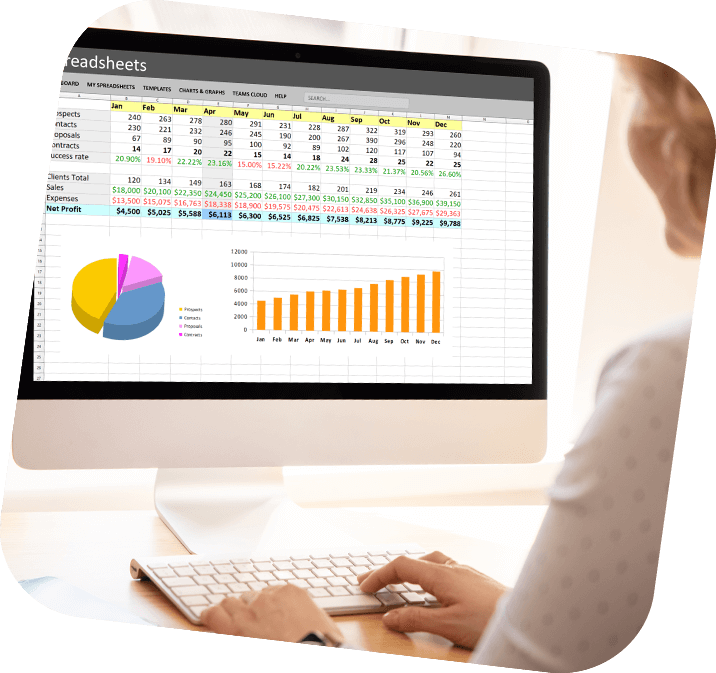
A third-party, Cloud-to-Cloud Backup is recommended for a business’s Office 365 data. This ensures complete, granular protection of your data with point-in-time retrieval, both scheduled and on-demand backup. It offers the flexibility to restore Teams, Exchange, SharePoint, and OneDrive data; deduplicate and compress data to maximise storage efficiency and minimize the backup window; identify and eliminate malware, viruses, and ransomware stored in SharePoint and OneDrive at the source
To stay ahead of cybercriminals, businesses need to protect data, users and systems. As per statistics, 91% of cyberattacks begin with a malicious email such as phishing, ransomware and spam. As these socially engineered attacks become more sophisticated and complex, businesses need to adopt a more people-centric approach.

Solutions today offer security teams complete cloud visibility in a single console and compliance report along with daily remediation.

Detect new threats (DNS) sooner, block malicious activities and data exfiltration attacks faster, and empower the total security stack with deeper intelligence. Providing leading networking security solutions that use DNS as a foundational security control, Infoblox delivers cloud-managed DNS, DHCP, IPAM and security services across private and hybrid, multi-cloud networks.

Identify security breaches and eliminate threats before they are exploited. A unified, cloud-based and cost-effective solution, Vicarius simplifies traditional vulnerability management that enables you to Patch vulnerabilities and deploy OS and software updates automatically and remotely.
SIEM systems gather and forward security-related events from end-user devices, servers and network equipment as well as specialised security equipment to a centralized management console. This is where the data is analysed to identify potential security issues and prioritise security incidents

Improving security posture, SOARs ingest alert data, and these alerts then trigger playbooks that automate/orchestrate response workflows or tasks. This allows organisations to respond swiftly to cybersecurity attacks besides enabling observation, understanding, and prevention of future incidents

Due to the costly SIEM solutions and a worldwide shortage of security professionals, organisations are increasingly turning to managed services to augment their SexOps team. Managed detection and response services and Extended Managed detection and response services can be deployed rapidly to identify and contain threats.

Monitoring, configuration management, Asset management, helpdesk tool, secure remote and much more is possible with Unified IT Infrastructure Management Solution. It helps Simplify Network & Systems Management across Heterogeneous IT Environments, on-premises and on cloud.

Shared security models of AWS/Azure often compromise business security, which has led customers to explore security solutions like Firewall, Server security, Patch management, Email security, CASBY and ATP on cloud platforms.


